Social engineering refers to the strategy of manipulating, influencing, or deceiving individuals with the intention of gaining control over a computer system or acquiring personal and financial information. This tactic relies on psychological manipulation to trick users into making security mistakes or divulging sensitive data.
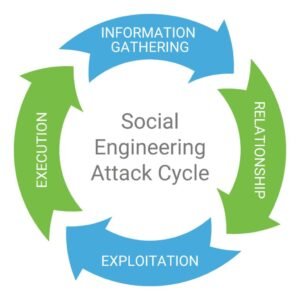
Social engineering attacks typically unfold in a series of steps. Initially, the perpetrator conducts thorough research on the target, collecting pertinent background information such as weak security protocols and potential entry points to facilitate their attack. Subsequently, the attacker adopts various forms of pretexting, like impersonation, to engender trust and elicit actions that undermine security practices, such as disclosing sensitive information or providing access to critical resources.
Various types of social engineering attacks exist. Here are some common examples:
Phishing: This involves masquerading as a trustworthy entity, usually via bulk emails, SMS texts, or phone calls, with the aim of acquiring sensitive information like usernames, passwords, or credit card details. Phishing messages often employ tactics such as urgency, curiosity, or fear to manipulate recipients into revealing confidential information, clicking on malicious links, or opening malware-infected attachments.
Baiting: In this form of attack, scammers entice victims with false promises, luring them into traps that may result in the theft of personal and financial information or the introduction of malware onto their systems. For instance, attackers may leave malware-infected flash drives in conspicuous areas, exploiting victims’ curiosity to prompt them into inserting these drives into their computers, consequently installing the malware.
Tailgating: Also known as “piggybacking,” this physical breach involves unauthorized individuals manipulating their way into restricted areas by employing social engineering tactics. Attackers may pose as delivery drivers or custodial workers, requesting assistance from employees to gain entry to the premises.
Scareware: This method deceives victims by bombarding them with false alarms and fictitious threats, creating the illusion that their systems are infected with malware. Consequently, users are prompted to install software that either grants remote access to criminals or coerces them into paying to safeguard sensitive data that the criminals claim to possess.
Dumpster Diving: Scammers search through improperly disposed garbage in search of sensitive information like bank statements, pre-approved credit cards, loan documents, or other account details.
Quid Pro Quo: In this type of attack, criminals entice victims with an exchange, offering a service in return for sensitive information such as critical data, login credentials, or monetary value. For instance, a criminal might impersonate a IT expert, contacting computer users and offering free IT assistance or enhancements in exchange for login credentials. Beware of offers that seem too good to be true, as they are likely scams.
Here are some tips to help avoid Social Engineering attacks:
- Exercise caution when opening email attachments from suspicious sources. If uncertain about the sender or suspicious of the message, confirm its authenticity by directly contacting the person directly.
- Utilize Multi-Factor Authentication (MFA) to safeguard user credentials, adding an extra layer of protection in the event of an account compromise.
- Remain vigilant regarding tempting offers. Research the legitimacy of offers that appear too good to be true, distinguishing between genuine opportunities and traps.
- Regularly review and clean up your social media presence. Social engineers scour the internet for personal information, so it’s essential to minimize the amount of information available that could be exploited in targeted attacks.
- Install and update antivirus software and other protective tools. Enable automatic updates and regularly scan your system for potential infections.
- Back up your data regularly. By creating backups on external hard drives or cloud storage, you minimize the impact of social engineering attacks that could corrupt your entire hard drive.
- Avoid plugging unknown USB drives, cables, and devices into your computer.
For more information on attack prevention or user education, contact PTS today!

